WordPress maintenance tends to focus on what's visible: the plugins you use regularly, the themes you update, the core version you're running. The risk that gets less attention is what's sitting quietly in the background, such as plugins that are no longer maintained, sometimes no longer even listed in the WordPress repository, but still installed and running on live sites.
These are what the security community has come to call zombie plugins. The term is a bit dramatic, but the problem is real. In 2024, Patchstack documented 1,614 plugins and themes removed from the WordPress.org repository for unpatched security issues. The vast majority, 1,450 of them, carried high- or medium-priority vulnerabilities. Most of those plugins didn't disappear from the sites where they were already installed. They just stopped getting patches.
This article covers what zombie plugins are, why WordPress's own infrastructure makes them harder to catch than you'd expect, and what a practical approach to managing them looks like.
What Are Zombie Plugins and Why Should You Care?
A zombie plugin is an abandoned WordPress plugin that remains active on a site after its developer has stopped maintaining it, or after it's been removed from the WordPress repository entirely. The plugin still runs. It still executes code on every page load. It just never receives another security update.
The risk isn't hypothetical. Patchstack found that 46% of vulnerabilities disclosed in 2025 hadn't been patched at the time of disclosure. For abandoned plugins, that number is effectively 100%; there's no developer left to release a fix, ever. An unpatched vulnerability in an active plugin is a known entry point for attackers, and without a developer maintaining it, it will never be fixed.
The plugin ecosystem makes this worse than it sounds. WordPress currently hosts over 60,000 free plugins, and a substantial portion haven't been meaningfully updated in years. During a single bug bounty event in October 2024, Patchstack researchers identified over 1,000 plugins with unpatched security issues, most of them abandoned, with developers who couldn't be reached.
Compatibility is a secondary concern, but worth noting. Abandoned plugins don't track WordPress core updates, which means they can conflict with active plugins or break functionality when core changes. Site owners often don't connect the dots between an old plugin and a performance or stability issue, which is part of what makes these quiet rather than obvious problems.
For organizations running WordPress as a business-critical platform, this isn't a theoretical risk to add to a list. It's an inventory problem that compounds quietly over time, and it tends to surface at the worst possible moment.
The Notification Gap WordPress Still Hasn't Fixed
Here's the part that surprises most site owners when they learn it: WordPress doesn't tell you when an installed plugin has been removed from the repository.
When a plugin gets pulled for security reasons, the WordPress admin dashboard continues to display it as up to date because there are no new updates available. There's no warning. No flag. No notification that the plugin has been closed, and the developer is unreachable. Patchstack has been raising this issue publicly since at least 2022. As of now, it remains unresolved in WordPress core.
This means sites can be running plugins that were quietly removed months or years ago, with no visible indicator that anything has changed. The only way to know is to check manually or have something in place that checks for you.
How to Identify Abandoned Plugins in Your WordPress Stack
The starting point is knowing what's actually installed on your site, and when it was last updated. This is something someone on your team or your agency should be doing on a regular, documented schedule. Anything that hasn't been updated in over a year warrants a closer look. Two years or more without an update, in most cases, is a signal that the plugin is no longer actively maintained.
From there, cross-reference each plugin against the WordPress Plugin Repository. A plugin that's been removed will show as unavailable. Community forums and the plugin's support page can also surface useful context patterns of unanswered security reports or extended developer silence, which are useful early signals.
The more reliable approach is to use tools built to audit WordPress installations systematically. These can scan your entire plugin inventory, flag outdated or abandoned components, and surface ones that have been removed from the repository. Running this kind of audit manually on an occasional basis is better than nothing; building it into a regular maintenance cycle is considerably better.
What Happens When These Plugins Are Exploited
Abandoned plugins don't just sit idle. Attackers actively target them, specifically because they know an unpatched plugin will never receive a fix.
In June 2024, five plugins hosted on WordPress.org were found to have been injected with malicious code, including Social Warfare, Blaze Widget, and Contact Form 7 Multi-Step Addon. The injected code created rogue administrative accounts and sent credentials to an attacker-controlled server. The attack affected tens of thousands of sites before it was caught.
The Display Widgets incident is an older but instructive example of a different attack vector. After its original developer sold the plugin, the new owners repeatedly added backdoor code across multiple versions. The plugin had over 200,000 active installations when it was finally permanently removed from the repository. WordPress.org removed it multiple times for violations before the final removal. Site owners had no way of knowing the plugin had been compromised unless they heard about it from a third-party source.
These aren't edge cases. They illustrate the two main ways zombie and abandoned plugins become attack vectors: through unpatched vulnerabilities that attackers scan for at scale, and through supply chain attacks that target the plugin distribution channel directly. In both cases, the site owner found out after the fact. That's the norm, not the exception, when nobody is actively watching the plugin layer.
Security Measures That Hold Up
The most direct mitigation is also the most obvious: remove plugins you're not actively using, and replace abandoned ones with maintained alternatives. An abandoned plugin with a known vulnerability is a permanently open door. Closing it requires removing the plugin, not finding a workaround.
Beyond removal, a few practices make a meaningful difference. Application-aware security tools that understand WordPress-specific vulnerability patterns, rather than generic firewall tools that weren't designed with WordPress in mind, are better positioned to catch plugin-targeted exploits. Virtual patching tools can deploy protection rules the moment a vulnerability is disclosed, blocking exploit attempts before a plugin developer has released a fix. For abandoned plugins, that gap is permanent, which makes this particularly relevant.
Regular plugin audits on a documented schedule matter more than one-time cleanups. The inventory shifts. New plugins get added. Developers abandon projects. A review that happens once and is never repeated creates a false sense of security that tends to be worse than no review at all.
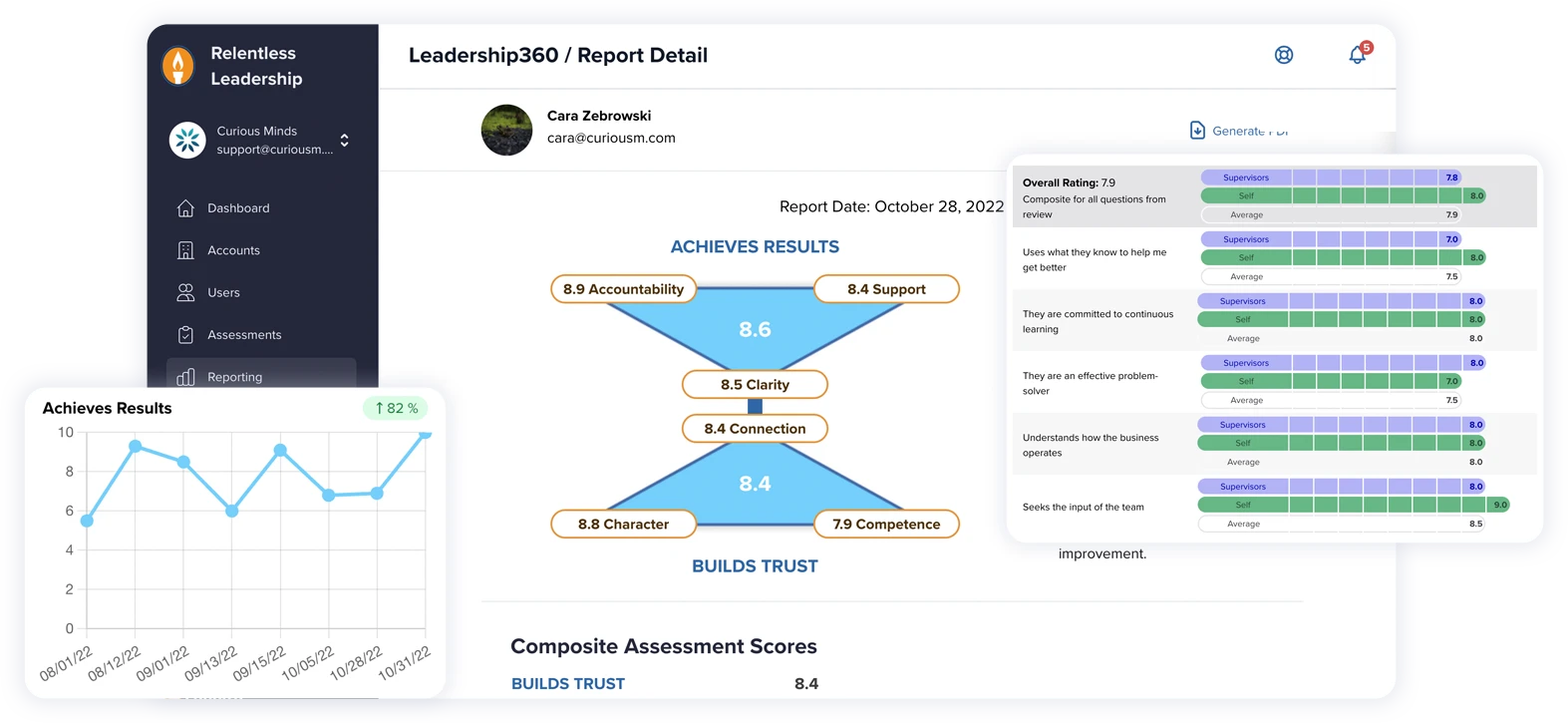
How Curious Minds Media Helps You Stay Secure and Up to Date
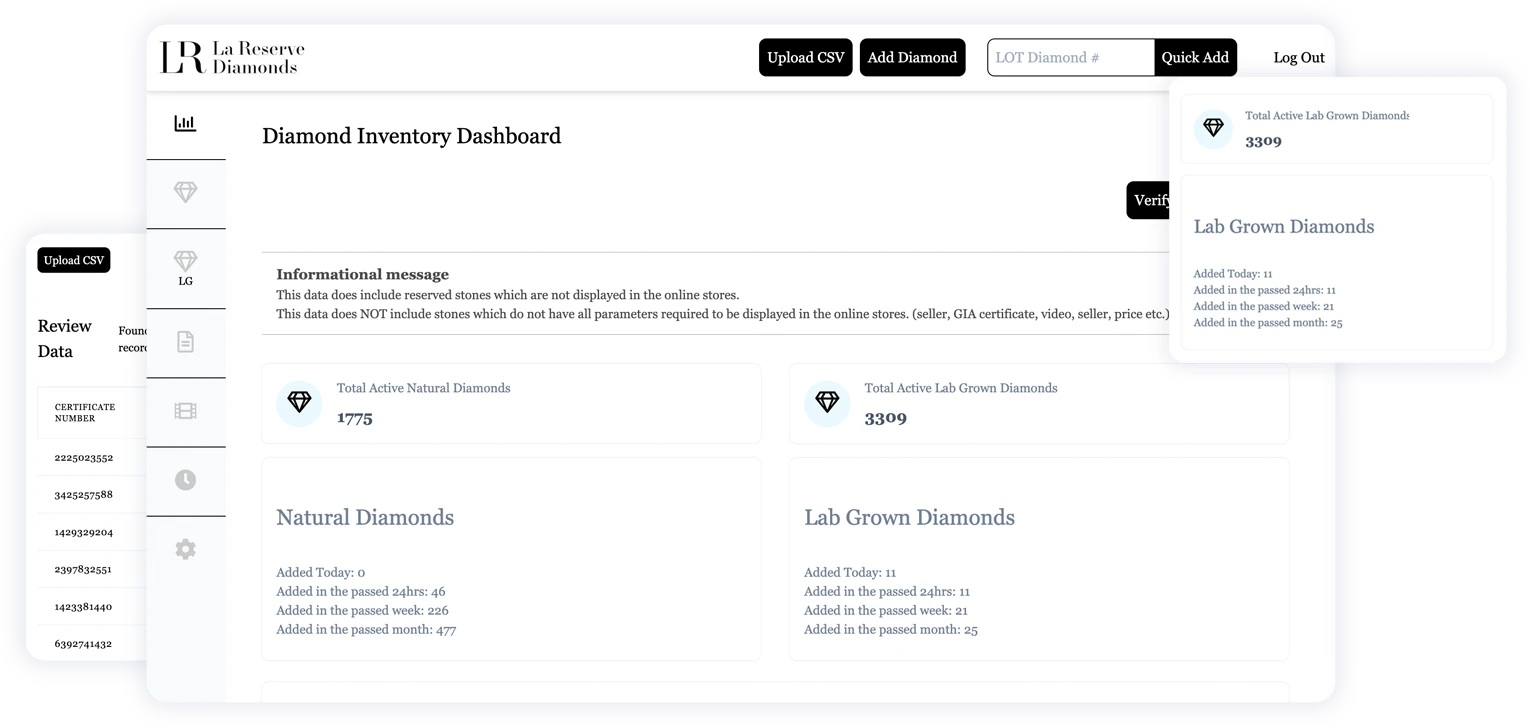
Plugin hygiene is a standard part of how we onboard and maintain WordPress sites at Curious Minds Media. When we take over a site, we run a full audit of what's installed, checking update history, repository status, and whether each plugin is still actively maintained. It's common to find plugins that have been running unattended for years, some of which have known vulnerabilities, some of which have been quietly removed from the repository.
For clients on ongoing maintenance plans, this is a recurring process rather than a one-time event. We track repository status, flag anything that's gone dormant, and help clients make decisions about replacement before something forces the issue.
If you're not sure what your current plugin inventory looks like or whether someone is actually watching it, that's usually a useful question to answer before it becomes an urgent one.
Regular Audits Prevent Costly Surprises
The WordPress security risk that tends to get the most attention is the active threat: the new vulnerability, the active exploit campaign, the zero-day. Zombie plugins represent a different kind of problem, one that accumulates gradually and doesn't announce itself until something goes wrong.
The organizations that manage this well aren't doing anything exotic. They know what's installed, they have a process for reviewing it regularly, and they remove things that are no longer maintained rather than leaving them in place indefinitely. That's most of what it takes.