Most WordPress security conversations focus on plugins, passwords, and patching. Those things matter. But the hosting infrastructure your site runs on quietly shapes your security posture in ways that only become visible when something goes wrong.
IP reputation is one of the least discussed and most consequential of those factors. When a WordPress site gets compromised, cleaned up, and put back online, the technical remediation is often the straightforward part. What follows is a different problem: the domain showing up on security vendor block lists, ISPs flagging the IP, visitors hitting warnings weeks after the malicious code is gone. The hack is fixed. The site is still blocked.
We see this pattern more than most people expect. The remediation gets done. The site is clean. But the IP reputation damage lingers, sometimes for months, because the infrastructure the site ran on didn't isolate it from the consequences of being flagged.
BigScoots' Cloudflare Enterprise integration, including dedicated IP capability through Cloudflare's Bring Your Own IP feature, addresses this directly. For organizations running WordPress sites where downtime, blacklisting, or access failures carry real business impact, understanding how IP reputation works and how hosting decisions affect it is worth the time.
Why IP Reputation Is a Hosting Problem
Most shared hosting environments put multiple sites on the same IP address. That's standard practice and causes no issues the vast majority of the time. The problem surfaces when one site in that shared environment gets compromised, starts sending spam, or gets flagged by a security vendor. The IP takes the hit. Every site sharing that IP takes the hit alongside it.
Restoring a flagged IP's reputation is slow by design. Major ISPs and security platforms don't move quickly, and the process of getting removed from block lists requires submitting requests to individual vendors, each on their own timeline. A site that was running clean can find itself blocked or filtered for months because of what happened to a neighbor on the same server.
For enterprise WordPress sites handling e-commerce transactions, lead generation, or business-critical communications, this is a real operational risk. The question isn't whether it can happen. It's whether your hosting configuration limits the damage when it does.
What Cloudflare's Security Layer Adds
Cloudflare sits between your site and incoming traffic, evaluating and filtering requests before they reach your server. The security benefits are well-established: DDoS mitigation that absorbs traffic floods designed to take sites offline, a web application firewall that blocks malicious requests at the network edge, and bot management that distinguishes real visitors from automated scanners and credential stuffers.
For WordPress sites, the bot management layer is particularly relevant. Automated attacks targeting WordPress login pages, xmlrpc.php endpoints, and known plugin vulnerabilities run continuously at scale. Cloudflare's network processes enough global traffic that it identifies and blocks these patterns faster than site-level defenses can respond.
The CDN layer delivers performance alongside security: content served from locations geographically closer to the visitor, reduced load on the origin server, faster page delivery across the board. For high-traffic WordPress sites, that's a meaningful operational benefit independent of the security considerations.
What Bring Your Own IP Actually Does
Standard Cloudflare configurations route traffic through Cloudflare's shared IP space. Your domain resolves to a Cloudflare IP, not your server's native IP, which provides origin protection. But that Cloudflare IP is still shared across Cloudflare's broader customer base.
Bring Your Own IP changes that. It allows organizations to use their own dedicated IP addresses within Cloudflare's network. Traffic still moves through Cloudflare's security and performance infrastructure, but over an IP that belongs exclusively to that organization. Sending reputation, delivery history, and standing with ISPs and security vendors are completely isolated from what other sites on the network are doing.
For organizations where IP reputation affects deliverability, transaction processing, or site accessibility, that isolation is the difference between a security incident affecting one site and a security incident affecting one site's relationship with every downstream system that evaluates IP reputation.
How BigScoots Enables This for WordPress Sites
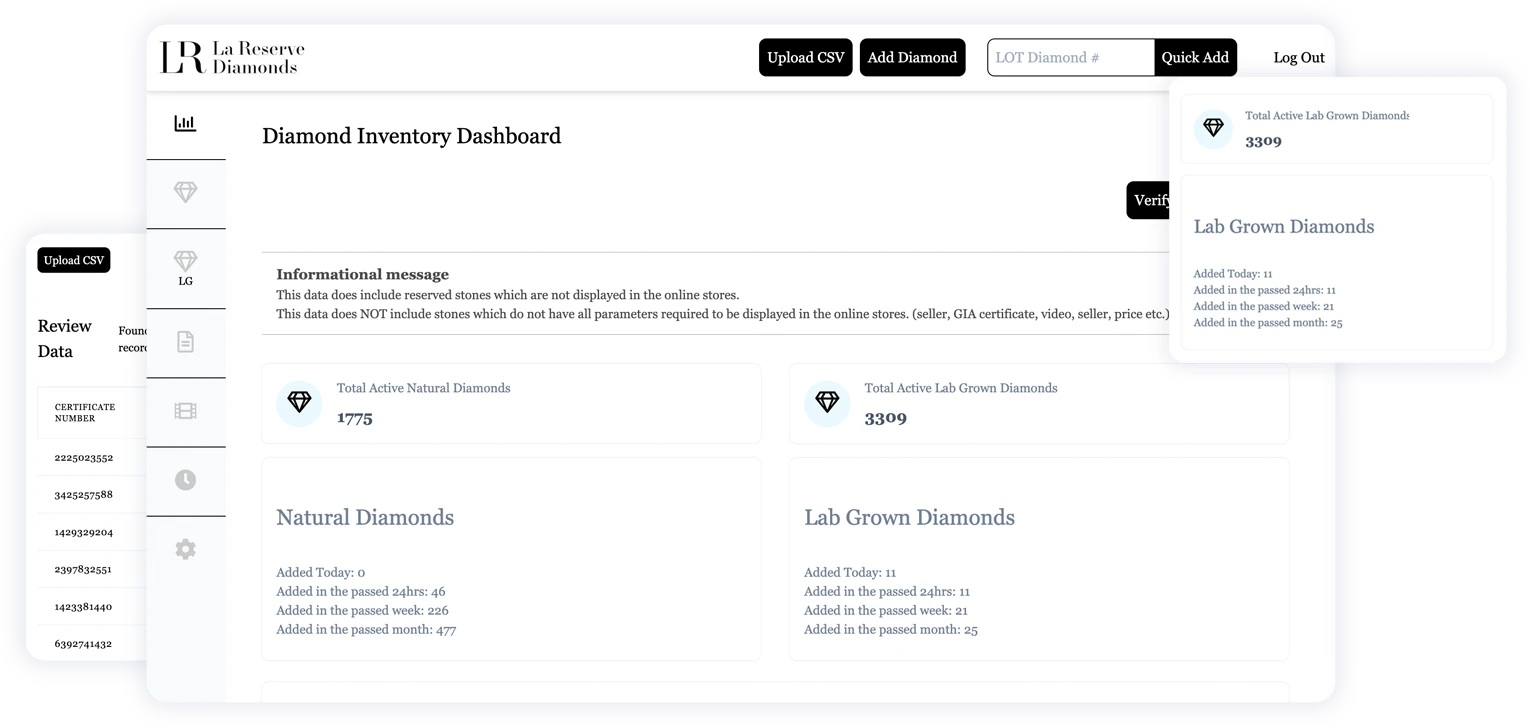
BigScoots is a managed WordPress hosting provider with over a decade of Cloudflare Enterprise partnership, building custom tooling and integrations on top of Cloudflare's infrastructure. Their Cloudflare Enterprise tier includes BYOIP capability alongside advanced security features: custom WAF rules, enterprise-grade DDoS mitigation, bot protection, and the full performance benefits of Cloudflare's global network.
We use BigScoots in our enterprise hosting stack for clients where performance, security, and IP reputation isolation matter. We've migrated clients to BigScoots specifically because the previous hosting environment was contributing to ongoing problems, and the move resolved issues that had persisted through other approaches. In a recent migration example, most of the issues that existed on their previous host cleared up after the move.
BigScoots also introduced IP geolocation data access through their Cloudflare Enterprise integration in early 2025, allowing sites to pull visitor location data directly from request headers without a third-party geolocation service. For e-commerce and marketing sites that personalize content by geography, that's a useful capability built into the hosting layer rather than added on top of it.
The Practical Case for Dedicated IP Infrastructure
Dedicated IP infrastructure doesn't prevent WordPress sites from getting hacked. Nothing does entirely. What it does is limit how far the consequences spread when something goes wrong. The IP reputation fallout from a security incident, the block lists, the ISP flags, the vendor queues, is often slower and more disruptive than the remediation itself. Hosting decisions that isolate your IP standing from shared infrastructure reduce that exposure before it becomes a problem, not after.
Hosting decisions and security decisions are the same conversation. The infrastructure your site runs on shapes your exposure in ways that only become obvious at the worst possible moment.
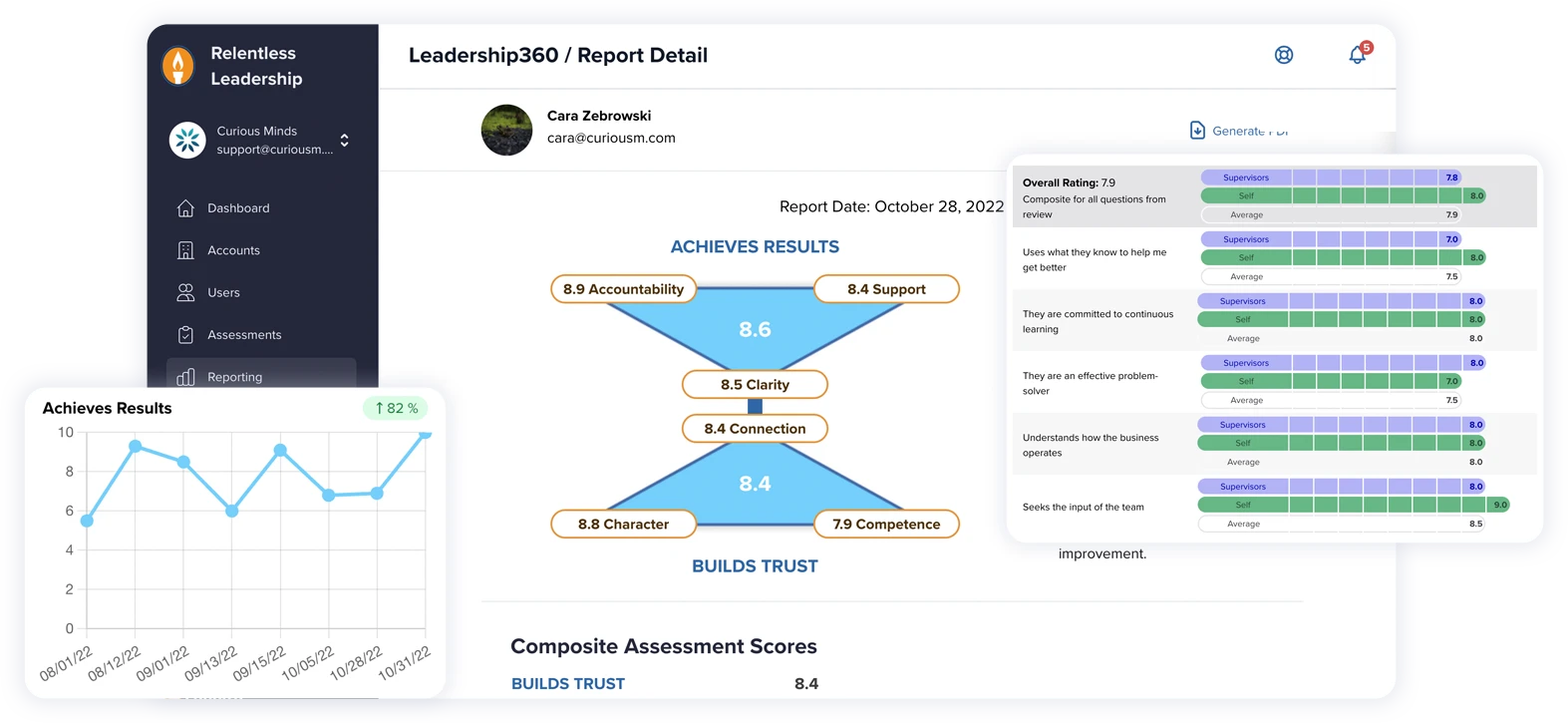
How Curious Minds Can Help
Hosting stack decisions are something we think through carefully with enterprise clients, because the right configuration depends on traffic profile, security requirements, and how much risk the business can absorb from different failure modes. If you're on shared hosting and haven't evaluated your IP reputation exposure, or if you've had a security incident and are still dealing with the downstream effects, we're happy to take a look at your current setup and talk through what makes sense.