Keeping your WordPress site secure and stable has always required staying on top of updates and running a reasonable set of defenses. That bar has moved significantly. Advanced AI now gives cybercriminals tools that operate faster, adapt more intelligently, and evade traditional detection methods at a scale that wasn't possible just a few years ago.
These aren't theoretical risks. Patchstack's 2026 State of WordPress Security report documented 11,334 new vulnerabilities in the WordPress ecosystem in 2025 alone, a 42% increase over 2024. More than half of the traffic hitting websites today isn't human, according to Imperva's 2025 Bad Bot Report. And the window between vulnerability disclosure and active exploitation has shrunk to a median of five hours.
For a business running WordPress as a revenue channel or lead generation platform, that window is an operational risk, not just a technical one. A compromised site doesn't just get cleaned up; it gets blacklisted by Google, loses customer trust, and in some cases goes down during the exact campaign or traffic spike it was built to support.
Understanding how these threats work and which defenses are still effective is the starting point for any serious approach to WordPress security.
AI Botnets: Smarter, Faster, and Harder to Detect
Traditional bots were blunt instruments. They hit login pages, ran through password lists, got blocked, and moved on. They worked because of volume, not intelligence.
AI-powered botnets operate differently. They use machine learning to mimic human browsing behavior convincingly enough to pass behavioral analysis tools. They rotate identities, adapt when one approach stops working, and target weaknesses with precision rather than brute force.
The CAPTCHA problem illustrates this clearly. In 2024, researchers at ETH Zurich published a study demonstrating that an AI model using advanced image recognition could solve Google's reCAPTCHA v2 challenges with a 100% success rate, compared to earlier systems that topped out around 68-71%. Commercial services now advertise similar success rates across reCAPTCHA v2/v3, hCaptcha, and Cloudflare Turnstile. CAPTCHAs haven't become useless, but they’re no longer a meaningful barrier for a motivated attacker.
The speed at which these attacks operate is the harder problem. Patchstack's data shows that for heavily exploited vulnerabilities, 20% are targeted within six hours of disclosure, 45% within 24 hours, and 70% within seven days. The weighted median time to first exploitation was five hours. That's five hours from the moment a vulnerability becomes public knowledge to the moment automated scanners are actively probing sites that haven't patched.
Why WordPress Sites Are a Primary Target
WordPress powers a significant share of the web, which makes it a consistently attractive target. But the core software itself isn't the primary vulnerability. Of the 11,334 vulnerabilities Patchstack documented in 2025, 91% came from plugins. Just two affected the WordPress core.
This matters because the plugin ecosystem is vast, variable in quality, and difficult to monitor comprehensively. Thousands of plugins exist in states of partial or complete abandonment. Patchstack found that 46% of vulnerabilities disclosed in 2025 hadn't been patched at the time of disclosure, meaning nearly half were publicly known while the affected plugin was still shipping vulnerable code.
Attackers understand this. They're not trying to break WordPress. They're scanning the plugin layer at scale, matching installed versions against known vulnerability databases, and running exploits against whatever they find. The approach is systematic and automated, not manual.
There's a newer dimension worth noting. AI coding tools are increasingly being used to build plugins, and research published in 2025 found that approximately 45% of code produced by current AI tools contains security flaws (See Vibe Coding). Patchstack has already identified vulnerabilities in AI-generated plugins that made it into active use. This is an expanding attack surface that lives entirely outside the normal plugin update and disclosure channels.
This is particularly relevant for organizations that have delegated website management to an agency or internal team. The assumption that someone else is watching the plugin layer, and watching it actively, not just responding to an incident, is often where the exposure lives. Knowing what's installed, who owns each plugin decision, and what the patching schedule actually looks like is a reasonable question for any leader to ask.
Security Measures That Still Work, and What Doesn't
Not every defense has become obsolete. But some have lost effectiveness in ways that aren't always obvious.
Static IP blocking and pattern-based detection struggle against AI-enhanced botnets that rotate identities and mimic legitimate user behavior. By the time a blocklist is updated or a signature is written, the bots have adapted. These tools still have value in a layered security setup, but depending on them as primary defenses is a significant gap.
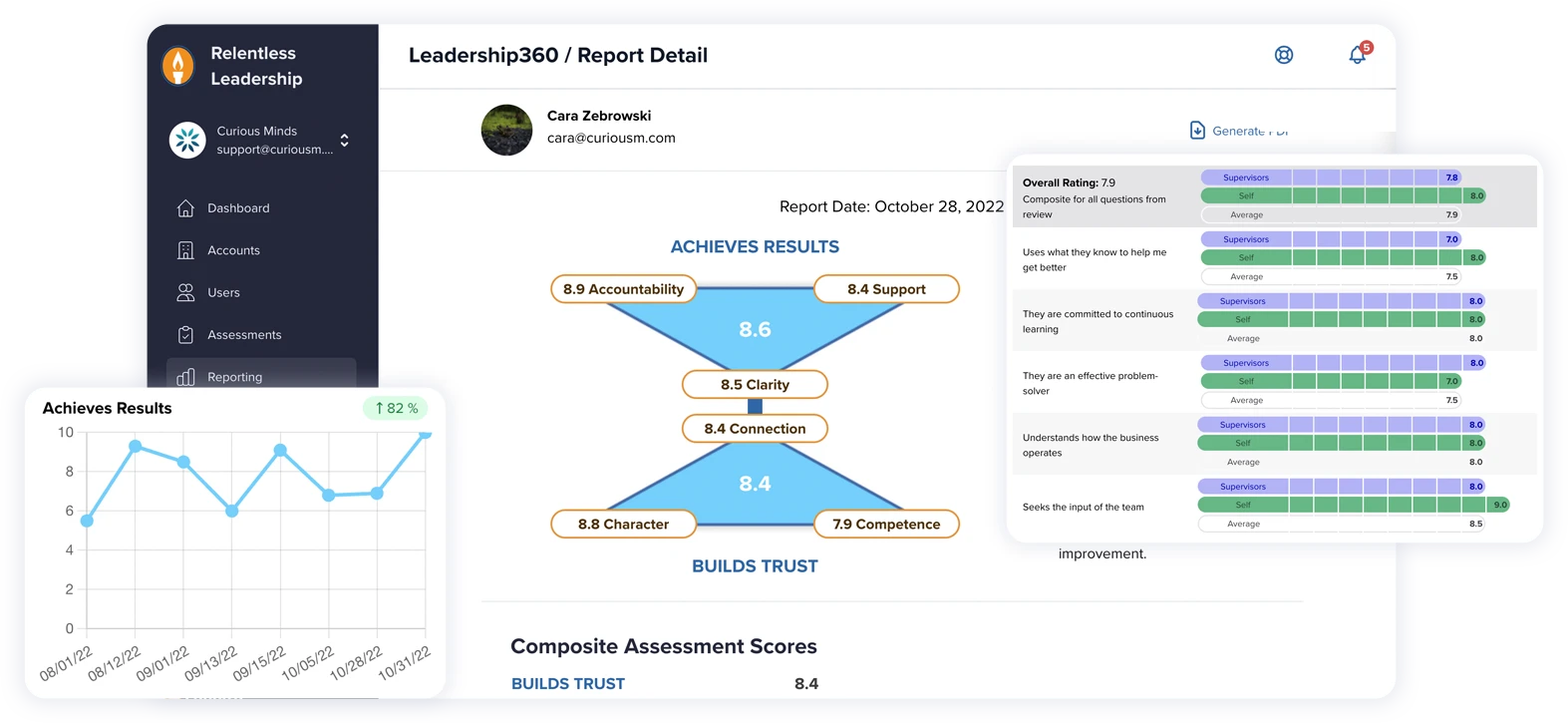
Patchstack's own pentesting studies in 2025 tested common security solutions, including hosting-level WAFs, Cloudflare, Imunify360, and ModSecurity, against real WordPress vulnerability exploits. Traditional defenses blocked just 12% of attacks when focused on known exploited vulnerabilities. One host blocked nothing. The poor results came largely from Broken Access Control attacks, which account for 57% of exploits and look like ordinary authenticated traffic, with no obvious injection patterns for generic rules to catch.
Traditional hosting defenses blocked just 12% of known-exploited vulnerability attacks in Patchstack's 2025 pentesting study. One host blocked nothing. -Patchstack, State of WordPress Security In 2026
What does hold up: application-aware protection that understands WordPress-specific threat patterns. Patchstack's virtual patching approach deploys exploit-blocking rules at the application layer the moment a vulnerability is disclosed, before a plugin vendor has released a fix. Two-factor authentication closes a significant credential attack surface; Wordfence blocked 55 billion credential attacks in 2024, and 2FA makes the ones that get through useless. And managed WordPress hosting with active monitoring narrows the window between exposure and response.
Plugin hygiene is unglamorous but genuinely high-impact. Removing unused, outdated, or abandoned plugins reduces the attack surface directly. An abandoned plugin with a known vulnerability will never receive a patch. Keeping it installed is a permanent open door.
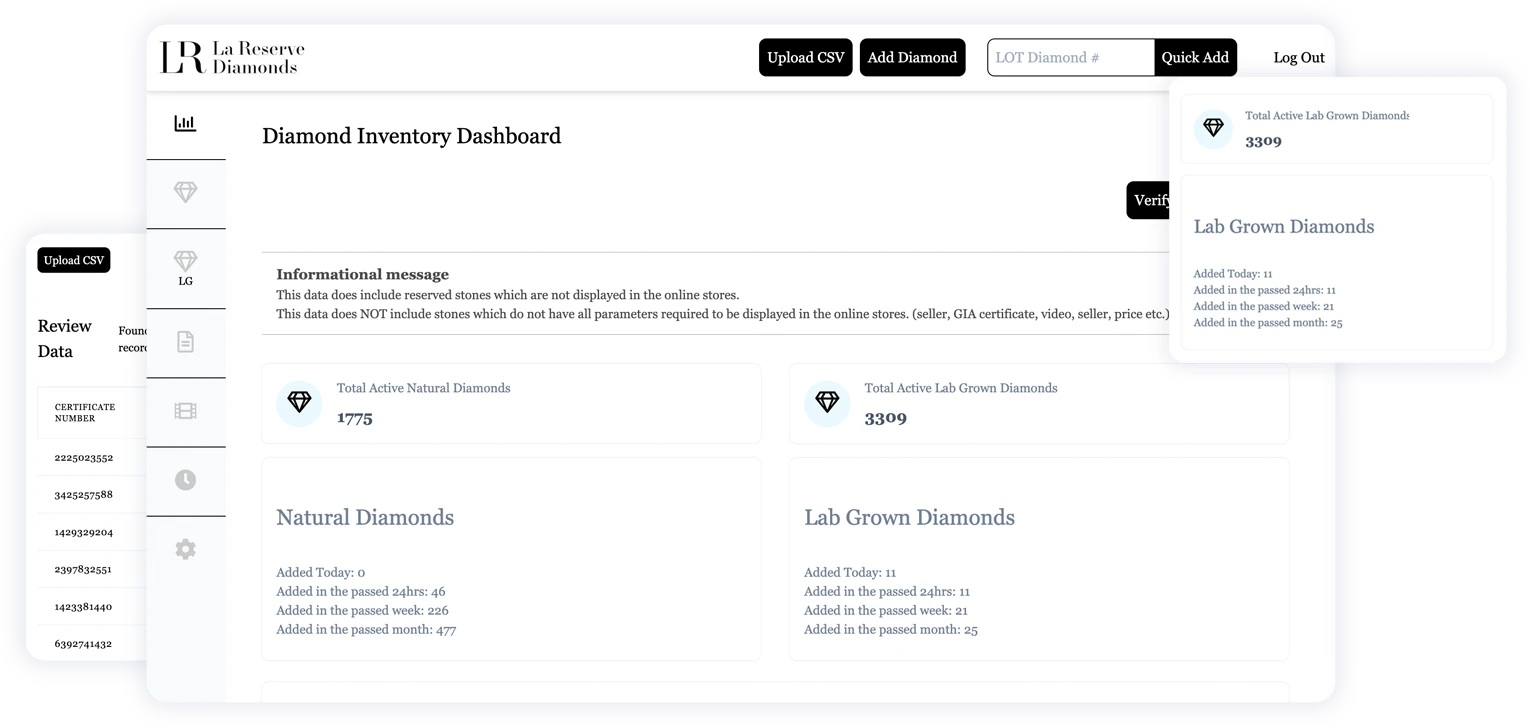
How Curious Minds Media Approaches WordPress Security
Security at Curious Minds Media isn't a product we bolt on at the end of a project. It's part of how we configure and maintain WordPress environments from the start because the evidence is clear that configuration and ongoing maintenance matter more than any individual security tool.
For clients on our maintenance plans, security is a shared responsibility that works best when both sides are communicating actively. We run scheduled patching and periodic plugin audits, but the reality of the threat landscape is that no maintenance schedule alone catches everything. Some of the most useful signals come from clients forwarding vulnerability notices they've received directly. That kind of transparency, a client flagging something they saw, us knowing the context of what's installed and why, is what actually closes the gap. Routine audits surface more exposure than most clients expect, but the relationship around security matters as much as the technical work.
If your current agency or hosting provider can't answer basic questions about your plugin inventory, patching cadence, or what they'd do in the first hour of a compromise, those are gaps worth taking seriously before something forces the conversation.
The Threat Environment Moves Faster Than Most Maintenance Schedules
A lot of WordPress security guidance ends with "keep everything updated" and a checklist. That advice isn't wrong, but it's no longer sufficient on its own. The organizations that get hit hardest aren't the ones that ignored security entirely. They're the ones where security was someone else's job and nobody checked whether that job was actually getting done.
AI has accelerated the pace at which defenses go stale. A setup that was solid in 2022 may have meaningful gaps today, not because the tools stopped working, but because the attacks evolved around them. The five-hour exploitation window makes that a concrete operational problem, not just a theoretical concern.